As part of my bug bounty work in 2020, I discovered a critical security issue affecting the Yuzo Related Posts plugin on WordPress. While this vulnerability was promptly patched and the case is now closed, it remains a valuable example of the importance of vigilant plugin management and proactive security.
Summary of the Stored XSS Vulnerability
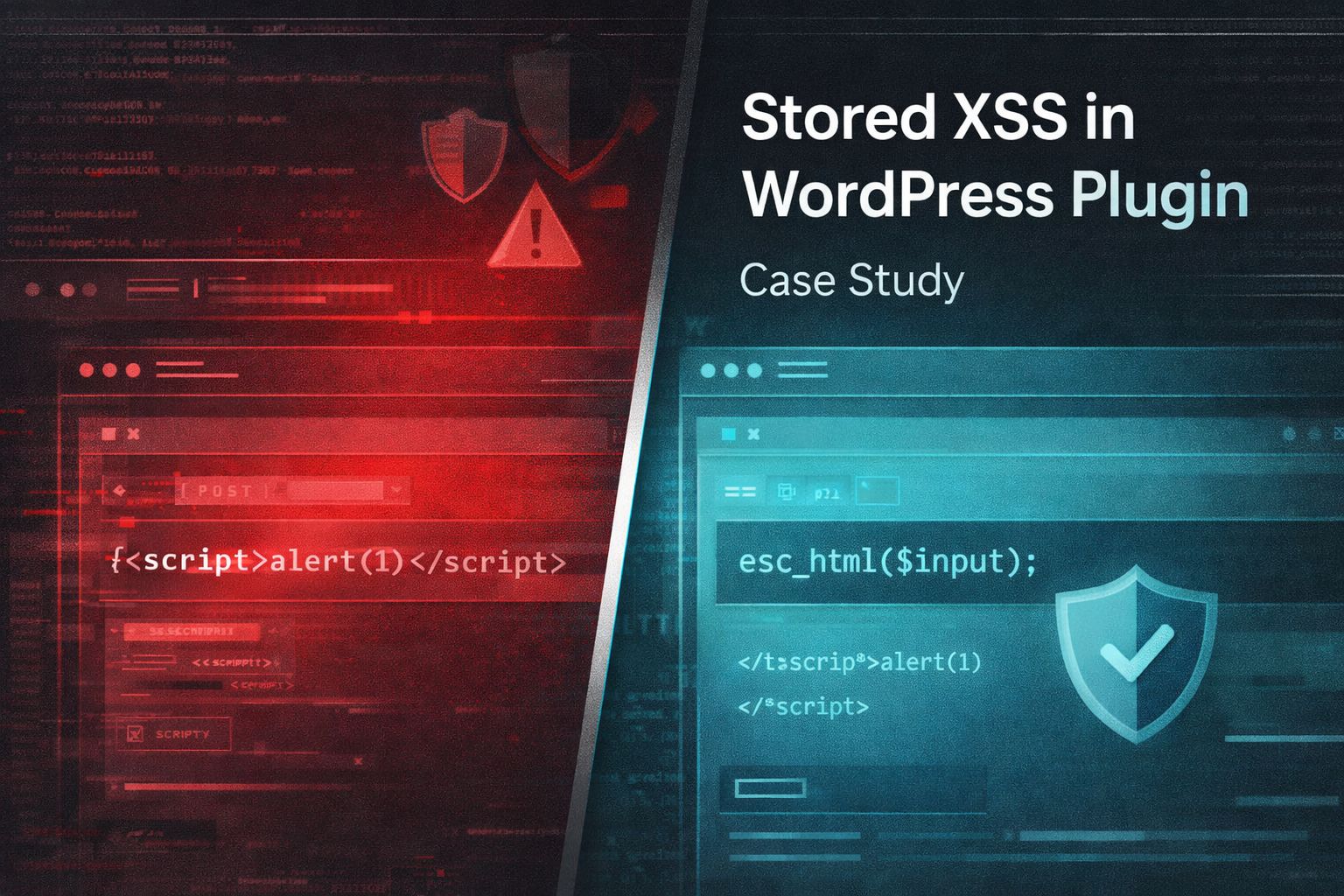
A Stored XSS vulnerability arises when user-supplied input is accepted and stored without proper sanitization, then output to users, allowing script execution in the browsers of anyone viewing the affected content.
In 2020, I found such a flaw within the settings menu of the Yuzo Related Posts plugin. This allowed attackers to inject JavaScript directly into the WordPress database, posing risks to both admins and visitors.
Thankfully, quick reporting and responsive patching ensured this issue was short-lived.
Vulnerability Details
Here are the core details as they appeared at the time:
- Website: https://ipage.com/blog
- Platform: WordPress 5.0.8
- Plugin: Yuzo Related Posts (v5.12.90)
- Type: Stored XSS (CWE-79)
- Severity: Medium (CVSS 6.1)
Where the Issue Was
The vulnerable endpoint:
/wp-admin/admin-post.php?page=yuzo-related-postThe vulnerable parameter:
yyuzo_related_post_top_textThis parameter accepts raw HTML input without proper sanitization.
Proof of Concept
A crafted POST request could inject arbitrary HTML or JavaScript:
<form action="https://ipage.com/blog/wp-admin/admin-post.php?page=yuzo-related-post" method="POST">
<input type="hidden" name="yyuzo_related_post_top_text" value="<script>alert(1)</script>" />
</form>If processed and rendered, the payload executes in the browser.
Why This Happens
This is a common WordPress plugin issue:
- Input is accepted from POST
- No sanitization (e.g., sanitize_text_field, wp_kses)
- Output is rendered directly
- Result: XSS
In this case, the root cause was an outdated plugin version.
Impact
An attacker could:
- Execute arbitrary JavaScript
- Hijack user sessions
- Inject malicious content into pages
- Redirect users to phishing pages
Even medium-severity XSS can become critical when:
- Admin users are targeted
- The payload persists
- It is combined with other vulnerabilities
Timeline
- Reported: January 1, 2020
- Verified: January 1, 2020
- Fixed: March 30, 2020
How It Was Fixed
The issue was resolved by updating the plugin:
- Vulnerable version: 5.12.90
- Fixed version: 5.12.94
How to Prevent This
1. Sanitize Input
sanitize_text_field($input);For HTML:
wp_kses_post($input);2. Escape Output
echo esc_html($data);Or:
echo wp_kses_post($data);3. Keep Plugins Updated
- Remove unused plugins
- Replace abandoned plugins
- Monitor known vulnerabilities
4. Avoid Storing Raw HTML
- Whitelist allowed tags
- Strip scripts
- Validate on input and output
Key Takeaway
This was not a complex exploit.
It was a basic input validation failure in an outdated plugin.
Most real-world compromises are caused by:
- Known vulnerabilities
- Outdated components
- Poor validation
Credits
Discovered and reported by:
Gerasimos Mourelatos (makismour)
Original report:
https://www.openbugbounty.org/reports/1055611/36e4d8de65ddeae882bfaee78743e00c/