Overview
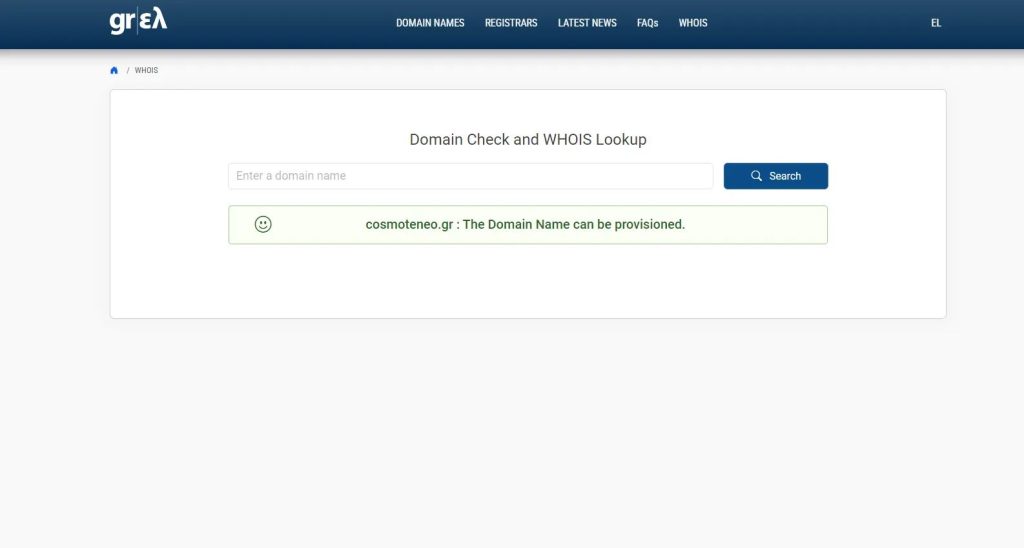
This report documents an unregistered domain exposure involving cosmoteneo.gr, a domain referenced in relation to Cosmote’s “Neo” service.
The domain was publicly referenced but had not been registered or reserved by the organization. As a result, it was available for acquisition and could have been controlled by any external party.
This type of issue does not rely on software vulnerabilities or exploitation techniques. It stems from gaps in asset management and domain ownership controls.
Technical Summary
- Affected Asset: cosmoteneo.gr
- Issue Type: Unregistered Domain Exposure / Domain Takeover Risk
- Attack Vector: Public domain registration
- Impact: Potential service impersonation, phishing, brand abuse
- Severity: High
Discovery
During routine analysis of publicly referenced assets, the domain cosmoteneo.gr was identified as associated with Cosmote’s Neo service.
Further checks confirmed that:
- The domain was not registered
- No ownership or reservation mechanism was in place
- The domain was available for public purchase
This created a direct opportunity for third parties to acquire and control the domain.
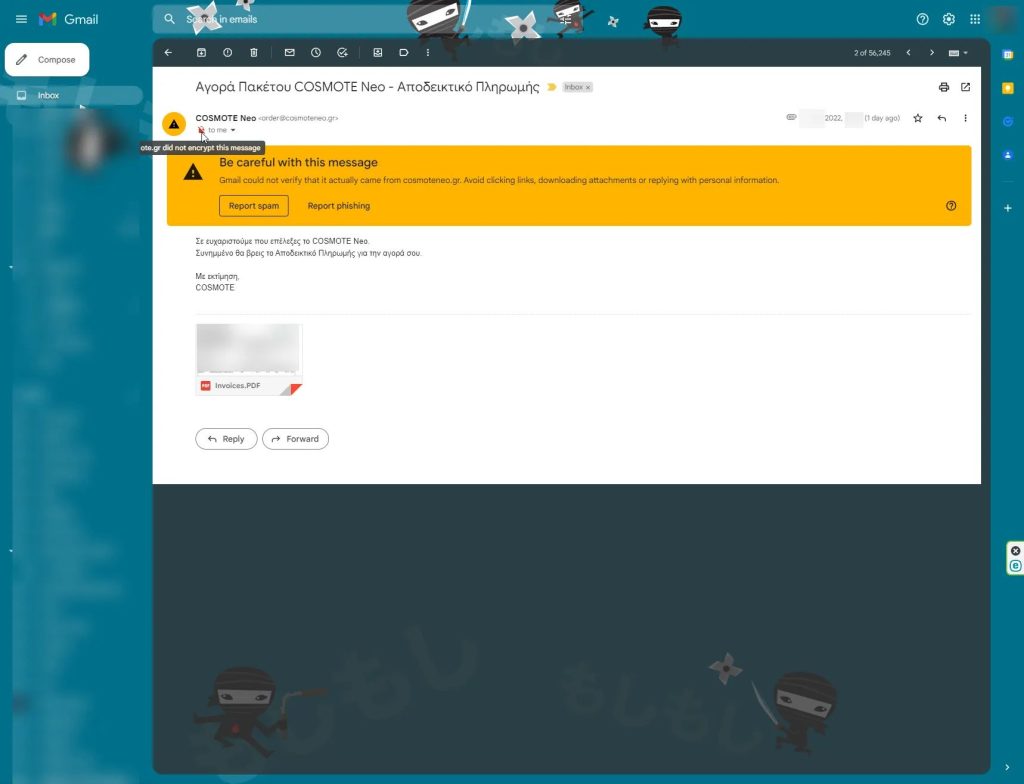
Proof of Control (Sanitized Evidence)
During validation, the domain allowed external service registration using a non-authorized email address.
Example identifier used during testing:
Delivered-To: [email protected]
Received: by 2002:a54:36d2:0:b0:1d8:bbce:41d6 with SMTP id x18csp40319ect;
Thu, xx xx 2022 xx:x:00 -0700 (PDT)
X-Google-Smtp-Source: AMsMyM7Dn3RApZzWs60So6QovjSwGaF23u8eFipOUd4AEnGJAQZU0aEV1G58o0MXzLTNd2x6KGo2
X-Received: by xx with SMTP id xx;
Thu, xx xx 2022 xx:xx:00 -0700 (PDT)
ARC-Seal: i=1; a=rsa-sha256; t=1663911960; cv=none;
d=google.com; s=arc-20160816;
b=Sar65ljYFxkKdbsirNoYZU9KdObwSpT/xbK4BrRd6D6iWNfwa+8BNvXqdQmrUYVy/0
XZhqFEuuVSSg8bY/1fxAFvbusckXd388wHf85ohslnDp22NTLh+ktOOr6jcjqR3J8pcm
jlWAbhOwhDq0L1np2RHzNujTkIWvFZXx29Yzide5I9d0xJG77YZA0nFkfxfVmSDyR1bu
gnSJn44vbwdvFpQpS9blalCDT+0Yh6ACbCl676DYqTgpgAu9bJTPBl3l668g7obVnQII
R8l0PeKz05T/8fUuBPXS9zqQOp8KRgX8AvSbeThgKBMpIwcRkEUF0lGNyh86F2bT/dpO
IpTg==
ARC-Message-Signature: i=1; a=rsa-sha256; c=relaxed/relaxed; d=google.com; s=arc-20160816;
h=importance:mime-version:message-id:to:subject:from:date;
bh=lpikMffdGQmJxSPoSiePN06c01vNZM7K6EpYfUty/go=;
b=X2+ORpgYCGugfojpuiHiHdgaSTCNA+S336HlJ0bhoUalUf22BM2Ah69LfOH8FNXf4o
kC8zzmWYWf88DgX2GbYiuSvGMtswhwtNQbBzs28EMi4zkPxvp5/nU+jgJg8sH2BN44Fq
oOESUkwe/pEPreNn2nu5VcyCx6zduYVQ/V3Vwixw6q2kPdNTDf7CbeEkGxpV19FEz72N
0M9RLI1BLf3/445Hzs0iF4svF7hgevTKkeRzhrguhwy/3JtQhtHEYUQ8d91reWxJSYxI
CN6MOjZiq2BJ+j1RtY3UFFO71xr9n/o0bon0aiQwKKctY+WVaNo+S9KSofobIFoqAjhH
HI7A==
ARC-Authentication-Results: i=1; mx.google.com;
spf=neutral (google.com: 212.205.80.57 is neither permitted nor denied by best guess record for domain of [email protected]) smtp.mailfrom=[email protected]
Return-Path: <[email protected]>
Received: from babbage.ote.gr (babbage.ote.gr. [212.205.80.57])
by mx.google.com with SMTP id xx.569.2022.09.22.22.45.50
for <[email protected]>;
Thu, 22 Sep 2022 22:46:00 -0700 (PDT)
Received-SPF: neutral (google.com: 212.205.80.57 is neither permitted nor denied by best guess record for domain of [email protected]) client-ip=212.205.80.57;
Authentication-Results: mx.google.com;
spf=neutral (google.com: 212.205.80.57 is neither permitted nor denied by best guess record for domain of [email protected]) smtp.mailfrom=[email protected]
Received: from babbage.ote.gr (unknown [127.0.0.1]) by IMSVA (Postfix) with ESMTP id 103A2B61E0 for <[email protected]>; xx, xx xx 2022 xx:xx:xx+0300 (EEST)
Received: from babbage.ote.gr (unknown [127.0.0.1]) by IMSVA (Postfix) with ESMTP id E5165B61B9 for <[email protected]>; xx, xx xx 2022 xx:xx:xx +0300 (EEST)
Received: from GERMANOS.GR (unknown [195.167.99.124]) by babbage.ote.gr (Postfix) with ESMTPS for <[email protected]>; xx, xx xx 2022 xx:xx:xx+0300 (EEST)
Date: xx, xx xx 2022 xx:xx:xx+0300 (EET)
From: COSMOTE Neo <[email protected]>
Subject: Αγορά Πακέτου COSMOTE Neo - Αποδεικτικό Πληρωμής
To: <[email protected]>
Message-ID: <[email protected]>
MIME-Version: 1.0
Importance: Normal
X-Priority: 3 (Normal)
X-Mailer: SAP NetWeaver 750
Content-Type: multipart/mixed; boundary="=xx"
X-TM-AS-GCONF: 00This confirms that the domain was neither reserved nor protected by the organization and could be claimed by an external party without verification of ownership.
Testing was performed in a controlled manner and strictly limited to validating exposure.
Impact
If acquired by a malicious actor, the domain could have been used for:
- Hosting phishing pages targeting Cosmote customers
- Sending fraudulent emails appearing as legitimate service communication
- Creating fake login portals or onboarding flows
- Damaging brand trust through impersonation
Because the domain appeared legitimate and contextually relevant, the likelihood of user trust and interaction would be high.
Root Cause
The issue originated from a breakdown in domain lifecycle and asset management processes.
Specifically:
- The domain was referenced publicly without being registered
- No defensive registration strategy was in place
- There was no monitoring to detect unclaimed or exposed assets
This is a governance issue rather than a technical flaw.
Responsible Disclosure
The issue was reported privately to the relevant parties with sufficient detail to reproduce and assess the risk.
The report focused on:
- Clear identification of the exposed domain
- Explanation of the takeover scenario
- Practical impact assessment
No exploitation beyond controlled validation was performed.
What This Means in Practice
This case is a reminder that not all security issues come from complex vulnerabilities.
Sometimes, exposure comes from something much simpler:
a domain that was referenced, but never actually secured.
From an attacker’s perspective, this is low effort with potentially high return.
There is no need to bypass protections or exploit software. The opportunity is already there.
From an operational standpoint, it highlights a gap that many organizations still have:
- Domains are mentioned in documentation, campaigns, or integrations
- But ownership and registration are not always verified
- Over time, these gaps accumulate and become exploitable
The fix is straightforward in theory, but requires consistency in practice:
- Maintain an accurate inventory of all domains tied to services
- Register or reserve domains before they are referenced publicly
- Periodically review exposed assets and remove anything unused
Securing all endpoints of an online service is, in most cases, not about advanced security tooling. It is about maintaining control over what you publish and expose by using the right frameworks to protect all endpoints before they even get published.
Closing Notes
Unregistered domain exposure remains a common and often overlooked risk. It does not require technical sophistication to exploit, yet it can have a direct impact on users and brand integrity.
Maintaining visibility over external assets and enforcing basic ownership controls is essential to reducing this type of risk.

